初次提交
This commit is contained in:
BIN
packages/BouncyCastle.Cryptography.2.2.1/.signature.p7s
vendored
Normal file
BIN
packages/BouncyCastle.Cryptography.2.2.1/.signature.p7s
vendored
Normal file
Binary file not shown.
BIN
packages/BouncyCastle.Cryptography.2.2.1/BouncyCastle.Cryptography.2.2.1.nupkg
vendored
Normal file
BIN
packages/BouncyCastle.Cryptography.2.2.1/BouncyCastle.Cryptography.2.2.1.nupkg
vendored
Normal file
Binary file not shown.
13
packages/BouncyCastle.Cryptography.2.2.1/LICENSE.md
vendored
Normal file
13
packages/BouncyCastle.Cryptography.2.2.1/LICENSE.md
vendored
Normal file
@@ -0,0 +1,13 @@
|
||||
Copyright (c) 2000-2023 The Legion of the Bouncy Castle Inc. (https://www.bouncycastle.org).
|
||||
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and
|
||||
associated documentation files (the "Software"), to deal in the Software without restriction,
|
||||
including without limitation the rights to use, copy, modify, merge, publish, distribute,
|
||||
sub license, and/or sell copies of the Software, and to permit persons to whom the Software is
|
||||
furnished to do so, subject to the following conditions: The above copyright notice and this
|
||||
permission notice shall be included in all copies or substantial portions of the Software.
|
||||
|
||||
**THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT
|
||||
NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND
|
||||
NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM,
|
||||
DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT
|
||||
OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.**
|
||||
45
packages/BouncyCastle.Cryptography.2.2.1/README.md
vendored
Normal file
45
packages/BouncyCastle.Cryptography.2.2.1/README.md
vendored
Normal file
@@ -0,0 +1,45 @@
|
||||
# The Bouncy Castle Cryptography Library For .NET
|
||||
[](https://www.nuget.org/packages/BouncyCastle.Cryptography) [](https://www.nuget.org/packages/BouncyCastle.Cryptography)
|
||||
|
||||
The Bouncy Castle Cryptography library is a .NET implementation of cryptographic algorithms and protocols. It was developed by the Legion of the Bouncy Castle, a registered Australian Charity, with a little help! The Legion, and the latest goings on with this package, can be found at [https://www.bouncycastle.org](https://www.bouncycastle.org).
|
||||
|
||||
In addition to providing basic cryptography algorithms, the package also provides support for CMS, OpenPGP, (D)TLS, TSP, X.509 certificate generation and more. The package also includes implementations of the following NIST Post-Quantum Cryptography Standardization algorithms: CRYSTALS-Dilithium, CRYSTALS-Kyber, Falcon, SPHINCS+, Classic McEliece, FrodoKEM, NTRU, NTRU Prime, Picnic, Saber, BIKE, and SIKE. These should all be considered EXPERIMENTAL and subject to change or removal. SIKE in particular is already slated for removal and should be used for research purposes only.
|
||||
|
||||
The Legion also gratefully acknowledges the contributions made to this package by others (see [here](https://www.bouncycastle.org/csharp/contributors.html) for the current list). If you would like to contribute to our efforts please feel free to get in touch with us or visit our [donations page](https://www.bouncycastle.org/donate), sponsor some specific work, or purchase a [support contract](https://www.keyfactor.com/platform/bouncy-castle-support/).
|
||||
|
||||
Except where otherwise stated, this software is distributed under a license based on the MIT X Consortium license. To view the license, [see here](https://www.bouncycastle.org/licence.html). This software includes a modified Bzip2 library, which is licensed under the [Apache Software License, Version 2.0](http://www.apache.org/licenses/).
|
||||
|
||||
**Note**: This source tree is not the FIPS version of the APIs - if you are interested in our FIPS version please visit us [here](https://www.bouncycastle.org/fips-csharp) or contact us directly at [office@bouncycastle.org](mailto:office@bouncycastle.org).
|
||||
|
||||
## Installing BouncyCastle
|
||||
You should install [BouncyCastle with NuGet:](https://www.nuget.org/packages/BouncyCastle.Cryptography)
|
||||
|
||||
Install-Package BouncyCastle.Cryptography
|
||||
|
||||
Or via the .NET Core command line interface:
|
||||
|
||||
dotnet add package BouncyCastle.Cryptography
|
||||
|
||||
Either commands, from Package Manager Console or .NET Core CLI, will download and install BouncyCastle.Cryptography.
|
||||
|
||||
|
||||
## Mailing Lists
|
||||
|
||||
For those who are interested, there are 2 mailing lists for participation in this project. To subscribe use the links below and include the word subscribe in the message body. (To unsubscribe, replace **subscribe** with **unsubscribe** in the message body)
|
||||
|
||||
* [announce-crypto-csharp-request@bouncycastle.org](mailto:announce-crypto-csharp-request@bouncycastle.org)
|
||||
This mailing list is for new release announcements only, general subscribers cannot post to it.
|
||||
* [dev-crypto-csharp-request@bouncycastle.org](mailto:dev-crypto-csharp-request@bouncycastle.org)
|
||||
This mailing list is for discussion of development of the package. This includes bugs, comments, requests for enhancements, questions about use or operation.
|
||||
|
||||
**NOTE:** You need to be subscribed to send mail to the above mailing list.
|
||||
|
||||
## Feedback
|
||||
|
||||
If you want to provide feedback directly to the members of **The Legion** then please use [feedback-crypto@bouncycastle.org](mailto:feedback-crypto@bouncycastle.org). If you want to help this project survive please consider [donating](https://www.bouncycastle.org/donate).
|
||||
|
||||
For bug reporting/requests you can report issues on [github](https://github.com/bcgit/bc-csharp), or via [feedback-crypto@bouncycastle.org](mailto:feedback-crypto@bouncycastle.org) if required. We will accept pull requests based on this repository as well, but only on the basis that any code included may be distributed under the [Bouncy Castle License](https://www.bouncycastle.org/licence.html).
|
||||
|
||||
## Finally
|
||||
|
||||
Enjoy!
|
||||
BIN
packages/BouncyCastle.Cryptography.2.2.1/lib/net461/BouncyCastle.Cryptography.dll
vendored
Normal file
BIN
packages/BouncyCastle.Cryptography.2.2.1/lib/net461/BouncyCastle.Cryptography.dll
vendored
Normal file
Binary file not shown.
29053
packages/BouncyCastle.Cryptography.2.2.1/lib/net461/BouncyCastle.Cryptography.xml
vendored
Normal file
29053
packages/BouncyCastle.Cryptography.2.2.1/lib/net461/BouncyCastle.Cryptography.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/BouncyCastle.Cryptography.2.2.1/lib/net6.0/BouncyCastle.Cryptography.dll
vendored
Normal file
BIN
packages/BouncyCastle.Cryptography.2.2.1/lib/net6.0/BouncyCastle.Cryptography.dll
vendored
Normal file
Binary file not shown.
29164
packages/BouncyCastle.Cryptography.2.2.1/lib/net6.0/BouncyCastle.Cryptography.xml
vendored
Normal file
29164
packages/BouncyCastle.Cryptography.2.2.1/lib/net6.0/BouncyCastle.Cryptography.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/BouncyCastle.Cryptography.2.2.1/lib/netstandard2.0/BouncyCastle.Cryptography.dll
vendored
Normal file
BIN
packages/BouncyCastle.Cryptography.2.2.1/lib/netstandard2.0/BouncyCastle.Cryptography.dll
vendored
Normal file
Binary file not shown.
29053
packages/BouncyCastle.Cryptography.2.2.1/lib/netstandard2.0/BouncyCastle.Cryptography.xml
vendored
Normal file
29053
packages/BouncyCastle.Cryptography.2.2.1/lib/netstandard2.0/BouncyCastle.Cryptography.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/BouncyCastle.Cryptography.2.2.1/packageIcon.png
vendored
Normal file
BIN
packages/BouncyCastle.Cryptography.2.2.1/packageIcon.png
vendored
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 32 KiB |
BIN
packages/Enums.NET.4.0.1/.signature.p7s
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/.signature.p7s
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/Enums.NET.4.0.1.nupkg
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/Enums.NET.4.0.1.nupkg
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/net45/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/net45/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/net45/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/net45/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
4788
packages/Enums.NET.4.0.1/lib/net45/Enums.NET.xml
vendored
Normal file
4788
packages/Enums.NET.4.0.1/lib/net45/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Enums.NET.4.0.1/lib/netcoreapp3.0/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netcoreapp3.0/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/netcoreapp3.0/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netcoreapp3.0/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
6289
packages/Enums.NET.4.0.1/lib/netcoreapp3.0/Enums.NET.xml
vendored
Normal file
6289
packages/Enums.NET.4.0.1/lib/netcoreapp3.0/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.0/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.0/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.0/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.0/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
4754
packages/Enums.NET.4.0.1/lib/netstandard1.0/Enums.NET.xml
vendored
Normal file
4754
packages/Enums.NET.4.0.1/lib/netstandard1.0/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.1/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.1/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.1/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.1/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
4764
packages/Enums.NET.4.0.1/lib/netstandard1.1/Enums.NET.xml
vendored
Normal file
4764
packages/Enums.NET.4.0.1/lib/netstandard1.1/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.3/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.3/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.3/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard1.3/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
4788
packages/Enums.NET.4.0.1/lib/netstandard1.3/Enums.NET.xml
vendored
Normal file
4788
packages/Enums.NET.4.0.1/lib/netstandard1.3/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.0/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.0/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.0/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.0/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
4788
packages/Enums.NET.4.0.1/lib/netstandard2.0/Enums.NET.xml
vendored
Normal file
4788
packages/Enums.NET.4.0.1/lib/netstandard2.0/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.1/Enums.NET.dll
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.1/Enums.NET.dll
vendored
Normal file
Binary file not shown.
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.1/Enums.NET.pdb
vendored
Normal file
BIN
packages/Enums.NET.4.0.1/lib/netstandard2.1/Enums.NET.pdb
vendored
Normal file
Binary file not shown.
4955
packages/Enums.NET.4.0.1/lib/netstandard2.1/Enums.NET.xml
vendored
Normal file
4955
packages/Enums.NET.4.0.1/lib/netstandard2.1/Enums.NET.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/MathNet.Numerics.Signed.4.15.0/.signature.p7s
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/.signature.p7s
vendored
Normal file
Binary file not shown.
BIN
packages/MathNet.Numerics.Signed.4.15.0/MathNet.Numerics.Signed.4.15.0.nupkg
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/MathNet.Numerics.Signed.4.15.0.nupkg
vendored
Normal file
Binary file not shown.
BIN
packages/MathNet.Numerics.Signed.4.15.0/icon.png
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/icon.png
vendored
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 12 KiB |
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/net40/MathNet.Numerics.dll
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/net40/MathNet.Numerics.dll
vendored
Normal file
Binary file not shown.
57672
packages/MathNet.Numerics.Signed.4.15.0/lib/net40/MathNet.Numerics.xml
vendored
Normal file
57672
packages/MathNet.Numerics.Signed.4.15.0/lib/net40/MathNet.Numerics.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/net461/MathNet.Numerics.dll
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/net461/MathNet.Numerics.dll
vendored
Normal file
Binary file not shown.
57672
packages/MathNet.Numerics.Signed.4.15.0/lib/net461/MathNet.Numerics.xml
vendored
Normal file
57672
packages/MathNet.Numerics.Signed.4.15.0/lib/net461/MathNet.Numerics.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard1.3/MathNet.Numerics.dll
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard1.3/MathNet.Numerics.dll
vendored
Normal file
Binary file not shown.
54300
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard1.3/MathNet.Numerics.xml
vendored
Normal file
54300
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard1.3/MathNet.Numerics.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard2.0/MathNet.Numerics.dll
vendored
Normal file
BIN
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard2.0/MathNet.Numerics.dll
vendored
Normal file
Binary file not shown.
57672
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard2.0/MathNet.Numerics.xml
vendored
Normal file
57672
packages/MathNet.Numerics.Signed.4.15.0/lib/netstandard2.0/MathNet.Numerics.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/.signature.p7s
vendored
Normal file
BIN
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/.signature.p7s
vendored
Normal file
Binary file not shown.
BIN
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/Microsoft.IO.RecyclableMemoryStream.2.3.2.nupkg
vendored
Normal file
BIN
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/Microsoft.IO.RecyclableMemoryStream.2.3.2.nupkg
vendored
Normal file
Binary file not shown.
279
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/README.md
vendored
Normal file
279
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/README.md
vendored
Normal file
@@ -0,0 +1,279 @@
|
||||
# Microsoft.IO.RecyclableMemoryStream [](https://www.nuget.org/packages/Microsoft.IO.RecyclableMemoryStream/)
|
||||
|
||||
A library to provide pooling for .NET `MemoryStream` objects to improve application performance, especially in the area of garbage collection.
|
||||
|
||||
## Get Started
|
||||
|
||||
Install the latest version from [NuGet](https://www.nuget.org/packages/Microsoft.IO.RecyclableMemoryStream/)
|
||||
|
||||
```
|
||||
Install-Package Microsoft.IO.RecyclableMemoryStream
|
||||
```
|
||||
|
||||
## Purpose
|
||||
|
||||
`Microsoft.IO.RecyclableMemoryStream` is a `MemoryStream` replacement that offers superior behavior for performance-critical systems. In particular it is optimized to do the following:
|
||||
|
||||
* Eliminate Large Object Heap allocations by using pooled buffers
|
||||
* Incur far fewer gen 2 GCs, and spend far less time paused due to GC
|
||||
* Avoid memory leaks by having a bounded pool size
|
||||
* Avoid memory fragmentation
|
||||
* Allow for multiple ways to read and write data that will avoid extraneous allocations
|
||||
* Provide excellent debuggability and logging
|
||||
* Provide metrics for performance tracking
|
||||
|
||||
## Features
|
||||
|
||||
- The semantics are close to the original `System.IO.MemoryStream` implementation, and is intended to be a drop-in replacement as much as possible.
|
||||
- Rather than pooling the streams themselves, the underlying buffers are pooled. This allows you to use the simple `Dispose` pattern to release the buffers back to the pool, as well as detect invalid usage patterns (such as reusing a stream after it’s been disposed).
|
||||
- `RecyclableMemoryStreamManager` is thread-safe (streams themselves are inherently NOT thread safe).
|
||||
- Implementation of `IBufferWrite<byte>`.
|
||||
- Support for enormous streams through abstracted buffer chaining.
|
||||
- Extensive support for newer memory-related types like `Span<byte>`, `ReadOnlySpan<byte>`, `ReadOnlySequence<byte>`, and `Memory<byte>`.
|
||||
- Each stream can be tagged with an identifying string that is used in logging - helpful when finding bugs and memory leaks relating to incorrect pool use.
|
||||
- Debug features like recording the call stack of the stream allocation to track down pool leaks
|
||||
- Maximum free pool size to handle spikes in usage without using too much memory.
|
||||
- Flexible and adjustable limits to the pooling algorithm.
|
||||
- Metrics tracking and events so that you can see the impact on the system.
|
||||
|
||||
## Build Targets
|
||||
|
||||
At least MSBuild 16.8 is required to build the code. You get this with Visual Studio 2019.
|
||||
|
||||
Supported build targets in v2.0 are: net462, netstandard2.0, netstandard2.1, and netcoreapp2.1 (net40, net45, net46 and netstandard1.4 were deprecated). Starting with v2.1, net5.0 target has been added.
|
||||
|
||||
## Testing
|
||||
|
||||
A minimum of .NET 5.0 is required for executing the unit tests. Requirements:
|
||||
- NUnit test adapter (VS Extension)
|
||||
- Be sure to set the default processor architecture for tests to x64 (or the giant allocation test will fail)
|
||||
|
||||
## Change Log
|
||||
|
||||
Read the change log [here](https://github.com/microsoft/Microsoft.IO.RecyclableMemoryStream/blob/master/CHANGES.md).
|
||||
|
||||
## How It Works
|
||||
|
||||
`RecyclableMemoryStream` improves GC performance by ensuring that the larger buffers used for the streams are put into the gen 2 heap and stay there forever. This should cause full collections to happen less frequently. If you pick buffer sizes above 85,000 bytes, then you will ensure these are placed on the large object heap, which is touched even less frequently by the garbage collector.
|
||||
|
||||
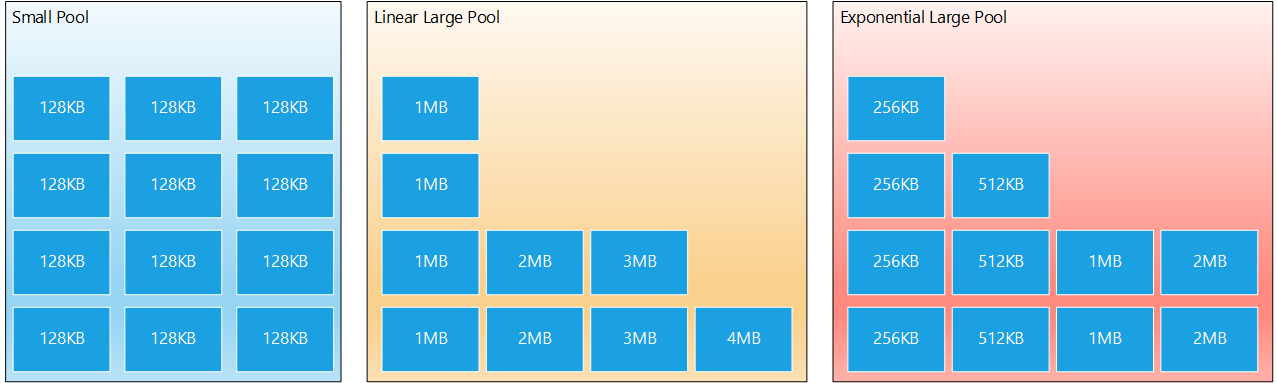
The `RecyclableMemoryStreamManager` class maintains two separate pools of objects:
|
||||
|
||||
1. **Small Pool** - Holds small buffers (of configurable size). Used by default for all normal read/write operations. Multiple small buffers are chained together in the `RecyclableMemoryStream` class and abstracted into a single stream.
|
||||
2. **Large Pool** - Holds large buffers, which are only used when you must have a single, contiguous buffer, such as when you plan to call `GetBuffer()`. It is possible to create streams larger than is possible to be represented by a single buffer because of .NET's array size limits.
|
||||
|
||||
A `RecyclableMemoryStream` starts out by using a small buffer, chaining additional ones as the stream capacity grows. Should you ever call `GetBuffer()` and the length is greater than a single small buffer's capacity, then the small buffers are converted to a single large buffer. You can also request a stream with an initial capacity; if that capacity is larger than the small pool block size, multiple blocks will be chained unless you call an overload with `asContiguousBuffer` set to true, in which case a single large buffer will be assigned from the start. If you request a capacity larger than the maximum poolable size, you will still get a stream back, but the buffers will not be pooled. (Note: This is not referring to the maximum array size. You can limit the poolable buffer sizes in `RecyclableMemoryStreamManager`)
|
||||
|
||||
There are two versions of the large pool:
|
||||
|
||||
* **Linear** (default) - You specify a multiple and a maximum size, and an array of buffers, from size (1 * multiple), (2 * multiple), (3 * multiple), ... maximum is created. For example, if you specify a multiple of 1 MB and maximum size of 8 MB, then you will have an array of length 8. The first slot will contain 1 MB buffers, the second slot 2 MB buffers, and so on.
|
||||
* **Exponential** - Instead of linearly growing, the buffers double in size for each slot. For example, if you specify a multiple of 256KB, and a maximum size of 8 MB, you will have an array of length 6, the slots containing buffers of size 256KB, 512KB, 1MB, 2MB, 4MB, and 8MB.
|
||||
|
||||
|
||||
|
||||
Which one should you use? That depends on your usage pattern. If you have an unpredictable large buffer size, perhaps the linear one will be more suitable. If you know that a longer stream length is unlikely, but you may have a lot of streams in the smaller size, picking the exponential version could lead to less overall memory usage (which was the reason this form was added).
|
||||
|
||||
Buffers are created, on demand, the first time they are requested and nothing suitable already exists in the pool. After use, these buffers will be returned to the pool through the `RecyclableMemoryStream`'s `Dispose` method. When that return happens, the `RecyclableMemoryStreamManager` will use the properties `MaximumFreeSmallPoolBytes` and `MaximumFreeLargePoolBytes` to determine whether to put those buffers back in the pool, or let them go (and thus be garbage collected). It is through these properties that you determine how large your pool can grow. If you set these to 0, you can have unbounded pool growth, which is essentially indistinguishable from a memory leak. For every application, you must determine through analysis and experimentation the appropriate balance between pool size and garbage collection.
|
||||
|
||||
If you forget to call a stream's `Dispose` method, this could cause a memory leak. To help you prevent this, each stream has a finalizer that will be called by the CLR once there are no more references to the stream. This finalizer will raise an event or log a message about the leaked stream.
|
||||
|
||||
Note that for performance reasons, the buffers are not ever pre-initialized or zeroed-out. It is your responsibility to ensure their contents are valid and safe to use buffer recycling.
|
||||
|
||||
## Usage
|
||||
|
||||
You can jump right in with no fuss by just doing a simple replacement of `MemoryStream` with something like this:
|
||||
|
||||
```csharp
|
||||
class Program
|
||||
{
|
||||
private static readonly RecyclableMemoryStreamManager manager = new RecyclableMemoryStreamManager();
|
||||
|
||||
static void Main(string[] args)
|
||||
{
|
||||
var sourceBuffer = new byte[] { 0, 1, 2, 3, 4, 5, 6, 7 };
|
||||
|
||||
using (var stream = manager.GetStream())
|
||||
{
|
||||
stream.Write(sourceBuffer, 0, sourceBuffer.Length);
|
||||
}
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
Note that `RecyclableMemoryStreamManager` should be declared once and it will live for the entire process lifetime. It is perfectly fine to use multiple pools if you desire, especially if you want to configure them differently.
|
||||
|
||||
To facilitate easier debugging, you can optionally provide a string `tag`, which serves as a human-readable identifier for the stream. This can be something like “ClassName.MethodName”, but it can be whatever you want. Each stream also has a GUID to provide absolute identity if needed, but the `tag` is usually sufficient.
|
||||
|
||||
```csharp
|
||||
using (var stream = manager.GetStream("Program.Main"))
|
||||
{
|
||||
stream.Write(sourceBuffer, 0, sourceBuffer.Length);
|
||||
}
|
||||
```
|
||||
|
||||
You can also provide an existing buffer. It’s important to note that the data from this buffer will be *copied* into a buffer owned by the pool:
|
||||
|
||||
```csharp
|
||||
var stream = manager.GetStream("Program.Main", sourceBuffer,
|
||||
0, sourceBuffer.Length);
|
||||
```
|
||||
|
||||
You can also change the parameters of the pool itself:
|
||||
|
||||
```csharp
|
||||
int blockSize = 1024;
|
||||
int largeBufferMultiple = 1024 * 1024;
|
||||
int maxBufferSize = 16 * largeBufferMultiple;
|
||||
|
||||
var manager = new RecyclableMemoryStreamManager(blockSize,
|
||||
largeBufferMultiple,
|
||||
maxBufferSize);
|
||||
|
||||
manager.GenerateCallStacks = true;
|
||||
manager.AggressiveBufferReturn = true;
|
||||
manager.MaximumFreeLargePoolBytes = maxBufferSize * 4;
|
||||
manager.MaximumFreeSmallPoolBytes = 100 * blockSize;
|
||||
```
|
||||
|
||||
### Usage Guidelines
|
||||
|
||||
While this library strives to be very general and not impose too many restraints on how you use it, its purpose is to reduce the cost of garbage collections incurred by frequent large allocations. Thus, there are some general guidelines for usage that may be useful to you:
|
||||
|
||||
1. Set the `blockSize`, `largeBufferMultiple`, `maxBufferSize`, `MaximumFreeLargePoolBytes` and `MaximumFreeSmallPoolBytes` properties to reasonable values for your application and resource requirements. **Important!**: If you do not set `MaximumFreeLargePoolBytes` and `MaximumFreeSmallPoolBytes` there is the possibility for unbounded memory growth!
|
||||
2. Always dispose of each stream exactly once.
|
||||
3. Most applications should not call `ToArray` and should avoid calling `GetBuffer` if possible. Instead, use `GetReadOnlySequence` for reading and the `IBufferWriter` methods `GetSpan`\\`GetMemory` with `Advance` for writing. There are also miscellaneous `CopyTo` and `WriteTo` methods that may be convenient. The point is to avoid creating unnecessary GC pressure where possible.
|
||||
4. Experiment to find the appropriate settings for your scenario.
|
||||
|
||||
A working knowledge of the garbage collector is a very good idea before you try to optimize your scenario with this library. An article such as [Garbage Collection](https://docs.microsoft.com/dotnet/standard/garbage-collection/), or a book like *Writing High-Performance .NET Code* will help you understand the design principles of this library.
|
||||
|
||||
When configuring the options, consider questions such as these:
|
||||
|
||||
* What is the distribution of stream lengths that I expect?
|
||||
* How many streams will be in use at one time?
|
||||
* Is `GetBuffer` called a lot? How much use of large pool buffers will I need?
|
||||
* How resilient to spikes in activity do I need to be? i.e., How many free bytes should I keep around in case?
|
||||
* What are my physical memory limitations on the machines where this will be used?
|
||||
|
||||
### IBufferWriter\<byte\>: GetMemory, GetSpan, and Advance ###
|
||||
|
||||
`RecyclableMemoryStream` implements [IBufferWriter<byte>](https://docs.microsoft.com/en-us/dotnet/api/system.buffers.ibufferwriter-1?view=netstandard-2.1) so it can be used for zero-copy encoding and formatting. You can also directly modify the stream contents using `GetSpan`\\`GetMemory` with `Advance`. For instance, writing a `BigInteger` to a stream:
|
||||
|
||||
```csharp
|
||||
var bigInt = BigInteger.Parse("123456789013374299100987654321");
|
||||
|
||||
using (var stream = manager.GetStream() as RecyclableMemoryStream)
|
||||
{
|
||||
Span<byte> buffer = stream.GetSpan(bigInt.GetByteCount());
|
||||
bigInt.TryWriteBytes(buffer, out int bytesWritten);
|
||||
stream.Advance(bytesWritten);
|
||||
}
|
||||
```
|
||||
|
||||
### GetReadOnlySequence ###
|
||||
|
||||
`GetReadOnlySequence` returns a [ReadOnlySequence<byte>](https://docs.microsoft.com/en-us/dotnet/api/system.buffers.readonlysequence-1?view=netstandard-2.1) that can be used for zero-copy stream processing. For example, hashing the contents of a stream:
|
||||
|
||||
```csharp
|
||||
using (var stream = manager.GetStream() as RecyclableMemoryStream)
|
||||
using (var sha256Hasher = IncrementalHash.CreateHash(HashAlgorithmName.SHA256))
|
||||
{
|
||||
foreach (var memory in stream.GetReadOnlySequence())
|
||||
{
|
||||
sha256Hasher.AppendData(memory.Span);
|
||||
}
|
||||
|
||||
sha256Hasher.GetHashAndReset();
|
||||
}
|
||||
```
|
||||
|
||||
### GetBuffer and ToArray ###
|
||||
|
||||
`RecyclableMemoryStream` is designed to operate primarily on chained small pool blocks. To access these blocks use `GetReadOnlySequence` for reading and `GetSpan`\\`GetMemory` with `Advance` for writing. However, if you still want a contiguous buffer for the whole stream there are two APIs which `RecyclableMemoryStream` overrides from its parent `MemoryStream` class:
|
||||
|
||||
* `GetBuffer` - If possible, a reference to the single block will be returned to the caller. If multiple blocks are in use, they will be converted into a single large pool buffer and the data copied into it. In all cases, the caller must use the `Length` property to determine how much usable data is actually in the returned buffer. If the stream length is longer than the maximum allowable stream size, a single buffer will still be returned, but it will not be pooled. If no possible contiguous buffer can be returned due to .NET array-size limitations, then an `OutOfMemoryException` will be thrown.
|
||||
* `ToArray` - It looks similar to `GetBuffer` on the surface, but is actually significantly different. In `ToArray` the data is *always* copied into a new array that is exactly the right length for the full contents of the stream. This new buffer is never pooled. Users of this library should consider any call to `ToArray` to be a bug, as it wipes out many of the benefits of `RecyclableMemoryStream` completely. However, the method is included for completeness, especially if you are calling other APIs that only take a `byte` array with no length parameter. An event is logged on all `ToArray` calls.
|
||||
|
||||
You can optionally configure the `RecyclableStreamManager.ThrowExceptionOnToArray` property to disallow calls to `RecyclableMemoryStream.ToArray`. If this value is set to true, then any calls to `ToArray` will result in a `NotSupportedException`.
|
||||
|
||||
## Metrics and Hooks
|
||||
|
||||
### ETW Events ###
|
||||
|
||||
`RecyclableMemoryStream` has an `EventSource` provider that produces a number of events for tracking behavior and performance. You can use events to debug leaks or subtle problems with pooled stream usage.
|
||||
|
||||
| Name | Level | Description |
|
||||
| -----|-------|-------------|
|
||||
| MemoryStreamCreated | Verbose | Logged every time a stream object is allocated. Fields: `guid`, `tag`, `requestedSize`, `actualSize`. |
|
||||
| MemoryStreamDisposed | Verbose | Logged every time a stream object is disposed. Fields: `guid`, `tag`, `allocationStack`, `disposeStack`. |
|
||||
| MemoryStreamDoubleDispose | Critical | Logged if a stream is disposed more than once. This indicates a logic error by the user of the stream. Dispose should happen exactly once per stream to avoid resource usage bugs. Fields: `guid`, `tag`, `allocationStack`, `disposeStack1`, `disposeStack2`. |
|
||||
| MemoryStreamFinalized | Error | Logged if a stream has gone out of scope without being disposed. This indicates a resource leak. Fields: `guid`, `tag`, `allocationStack`.|
|
||||
| MemoryStreamToArray | Verbose | Logged whenever `ToArray` is called. This indicates a potential problem, as calling `ToArray` goes against the concepts of good memory practice which `RecyclableMemoryStream` is trying to solve. Fields: `guid`, `tag`, `stack`, `size`.|
|
||||
| MemoryStreamManagerInitialized| Informational | Logged when the `RecyclableMemoryStreamManager` is initialized. Fields: `blockSize`, `largeBufferMultiple`, `maximumBufferSize`.|
|
||||
| MemoryStreamNewBlockCreated | Verbose | Logged whenever a block for the small pool is created. Fields: `smallPoolInUseBytes`.|
|
||||
| MemoryStreamNewLargeBufferCreated | Verbose | Logged whenever a large buffer is allocated. Fields: `requiredSize`, `largePoolInUseBytes`.|
|
||||
| MemoryStreamNonPooledLargeBufferCreated | Verbose | Logged whenever a buffer is requested that is larger than the maximum pooled size. The buffer is still created and returned to the user, but it can not be re-pooled. Fields: `guid`, `tag`, `requiredSize`, `allocationStack`. |
|
||||
| MemoryStreamDiscardBuffer | Warning | Logged whenever a buffer is discarded rather than put back in the pool. Fields: `guid`, `tag`, `bufferType` (`Small`, `Large`), `reason` (`TooLarge`, `EnoughFree`). |
|
||||
| MemoryStreamOverCapacity | Error | Logged whenever an attempt is made to set the capacity of the stream beyond the limits of `RecyclableMemoryStreamManager.MaximumStreamCapacity`, if such a limit is set. Fields: `guid`, `tag`, `requestedCapacity`, `maxCapacity`, `allocationStack`.|
|
||||
|
||||
### Event Hooks ###
|
||||
|
||||
In addition to the logged ETW events, there are a number of .NET event hooks on `RecyclableMemoryStreamManager` that you can use as triggers for your own custom actions:
|
||||
|
||||
| Name | Description |
|
||||
|---------|------------|
|
||||
| `BlockCreated` | A new small pool block has been allocated. |
|
||||
| `BufferDiscarded` | A buffer has been refused re-entry to the pool and given over to the garbage collector. |
|
||||
| `LargeBufferCreated` | A large buffer has been allocated. |
|
||||
| `StreamCreated` | A new stream has been created. |
|
||||
| `StreamDisposed` | A stream has been disposed. |
|
||||
| `StreamDoubleDisposed` | A stream has been disposed twice, indicating an error. |
|
||||
| `StreamFinalized` | A stream has been finalized, which means it was never disposed before it went out of scope. |
|
||||
| `StreamLength` | Reports the stream's length upon disposal. Can allow you to track stream metrics. |
|
||||
| `StreamConvertedToArray` | Someone called `ToArray` on a stream. |
|
||||
| `StreamOverCapacity` | An attempt was made to expand beyond the maximum capacity allowed by the pool manager. |
|
||||
| `UsageReport` | Provides stats on pool usage for metrics tracking. |
|
||||
|
||||
## Debugging Problems
|
||||
|
||||
Once you start introducing re-usable resources like the pooled buffers in `RecyclableMemoryStream`, you are taking some of the duties of the CLR away from it and reserving them for yourself. This can be error-prone. See the Usage section above for some guidelines on making your usage of this library successful.
|
||||
|
||||
There are a number of features that will help you debug usage of these streams.
|
||||
|
||||
### Stream Identification ###
|
||||
|
||||
Each stream is assigned a unique GUID and, optionally, a `tag`.
|
||||
|
||||
The GUID is unique for each stream object and serves to identify that stream throughout its lifetime.
|
||||
|
||||
A `tag` is an optional, arbitrary string assigned by the caller when a stream is requested. This can be a class name, function name, or some other meaningful string that can help you identify the source of the stream's usage. Note that multiple streams will contain the same tag. They identify where in your code the stream originated; they are not unique stream identifiers.
|
||||
|
||||
### Callstack Recording ###
|
||||
|
||||
If you set the `GenerateCallStacks` property on `RecyclableMemoryStreamManager` to true, then major operations on the stream, such as allocation and disposal, will record the call stack of those method calls. These will be reported in ETW events in the event of detected programming errors such as double-dispose or finalization.
|
||||
|
||||
Turning this feature on causes a very significant negative performance impact, so should only be done when actively investigating a problem.
|
||||
|
||||
### Double-Dispose Protection ###
|
||||
|
||||
If `Dispose` is called twice on the same stream, an event is logged with the relevant stream's information. If `GenerateCallStacks` is turned on, this will include the call stacks for allocation and both disposals.
|
||||
|
||||
### Non-Dispose Detection ###
|
||||
|
||||
If `Dispose` is never called for a stream, the finalizer will eventually be called by the CLR, and an event will be logged with relevant stream information, including the allocation stack, if enabled. Buffers for finalized streams are lost to the pool, and this should be considered a bug.
|
||||
|
||||
### Concurrency
|
||||
|
||||
Concurrent use of `RecyclableMemoryStream` objects is not supported under any circumstances. However, `RecyclableMemoryStreamManager` is thread-safe and can be used to retrieve streams in a multi-threading scenario.
|
||||
|
||||
### ETW Events ###
|
||||
|
||||
Use an ETW event monitor such as [PerfView](https://www.microsoft.com/download/details.aspx?id=28567) to collect and analyze ETW events.
|
||||
|
||||
Many of these events contain helpful clues about the stream in question, including its tag, guid, and stacks (if enabled).
|
||||
|
||||
## Reference
|
||||
|
||||
Read the API documentation [here](https://github.com/microsoft/Microsoft.IO.RecyclableMemoryStream/blob/master/docs/Microsoft.IO.RecyclableMemoryStream.md).
|
||||
|
||||
## License
|
||||
|
||||
This library is released under the [MIT license](https://github.com/microsoft/Microsoft.IO.RecyclableMemoryStream/blob/master/LICENSE).
|
||||
Binary file not shown.
1622
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/lib/net462/Microsoft.IO.RecyclableMemoryStream.xml
vendored
Normal file
1622
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/lib/net462/Microsoft.IO.RecyclableMemoryStream.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
Binary file not shown.
1625
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/lib/net5.0/Microsoft.IO.RecyclableMemoryStream.xml
vendored
Normal file
1625
packages/Microsoft.IO.RecyclableMemoryStream.2.3.2/lib/net5.0/Microsoft.IO.RecyclableMemoryStream.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
Binary file not shown.
File diff suppressed because it is too large
Load Diff
Binary file not shown.
File diff suppressed because it is too large
Load Diff
Binary file not shown.
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/.signature.p7s
vendored
Normal file
BIN
packages/NPOI.2.6.2/.signature.p7s
vendored
Normal file
Binary file not shown.
177
packages/NPOI.2.6.2/LICENSE
vendored
Normal file
177
packages/NPOI.2.6.2/LICENSE
vendored
Normal file
@@ -0,0 +1,177 @@
|
||||
Apache License
|
||||
Version 2.0, January 2004
|
||||
http://www.apache.org/licenses/
|
||||
|
||||
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
|
||||
|
||||
1. Definitions.
|
||||
|
||||
"License" shall mean the terms and conditions for use, reproduction, and
|
||||
distribution as defined by Sections 1 through 9 of this document.
|
||||
|
||||
"Licensor" shall mean the copyright owner or entity authorized by the copyright
|
||||
owner that is granting the License.
|
||||
|
||||
"Legal Entity" shall mean the union of the acting entity and all other entities
|
||||
that control, are controlled by, or are under common control with that entity.
|
||||
For the purposes of this definition, "control" means (i) the power, direct or
|
||||
indirect, to cause the direction or management of such entity, whether by
|
||||
contract or otherwise, or (ii) ownership of fifty percent (50%) or more of the
|
||||
outstanding shares, or (iii) beneficial ownership of such entity.
|
||||
|
||||
"You" (or "Your") shall mean an individual or Legal Entity exercising
|
||||
permissions granted by this License.
|
||||
|
||||
"Source" form shall mean the preferred form for making modifications, including
|
||||
but not limited to software source code, documentation source, and configuration
|
||||
files.
|
||||
|
||||
"Object" form shall mean any form resulting from mechanical transformation or
|
||||
translation of a Source form, including but not limited to compiled object code,
|
||||
generated documentation, and conversions to other media types.
|
||||
|
||||
"Work" shall mean the work of authorship, whether in Source or Object form, made
|
||||
available under the License, as indicated by a copyright notice that is included
|
||||
in or attached to the work (an example is provided in the Appendix below).
|
||||
|
||||
"Derivative Works" shall mean any work, whether in Source or Object form, that
|
||||
is based on (or derived from) the Work and for which the editorial revisions,
|
||||
annotations, elaborations, or other modifications represent, as a whole, an
|
||||
original work of authorship. For the purposes of this License, Derivative Works
|
||||
shall not include works that remain separable from, or merely link (or bind by
|
||||
name) to the interfaces of, the Work and Derivative Works thereof.
|
||||
|
||||
"Contribution" shall mean any work of authorship, including the original version
|
||||
of the Work and any modifications or additions to that Work or Derivative Works
|
||||
thereof, that is intentionally submitted to Licensor for inclusion in the Work
|
||||
by the copyright owner or by an individual or Legal Entity authorized to submit
|
||||
on behalf of the copyright owner. For the purposes of this definition,
|
||||
"submitted" means any form of electronic, verbal, or written communication sent
|
||||
to the Licensor or its representatives, including but not limited to
|
||||
communication on electronic mailing lists, source code control systems, and
|
||||
issue tracking systems that are managed by, or on behalf of, the Licensor for
|
||||
the purpose of discussing and improving the Work, but excluding communication
|
||||
that is conspicuously marked or otherwise designated in writing by the copyright
|
||||
owner as "Not a Contribution."
|
||||
|
||||
"Contributor" shall mean Licensor and any individual or Legal Entity on behalf
|
||||
of whom a Contribution has been received by Licensor and subsequently
|
||||
incorporated within the Work.
|
||||
|
||||
2. Grant of Copyright License.
|
||||
|
||||
Subject to the terms and conditions of this License, each Contributor hereby
|
||||
grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free,
|
||||
irrevocable copyright license to reproduce, prepare Derivative Works of,
|
||||
publicly display, publicly perform, sublicense, and distribute the Work and such
|
||||
Derivative Works in Source or Object form.
|
||||
|
||||
3. Grant of Patent License.
|
||||
|
||||
Subject to the terms and conditions of this License, each Contributor hereby
|
||||
grants to You a perpetual, worldwide, non-exclusive, no-charge, royalty-free,
|
||||
irrevocable (except as stated in this section) patent license to make, have
|
||||
made, use, offer to sell, sell, import, and otherwise transfer the Work, where
|
||||
such license applies only to those patent claims licensable by such Contributor
|
||||
that are necessarily infringed by their Contribution(s) alone or by combination
|
||||
of their Contribution(s) with the Work to which such Contribution(s) was
|
||||
submitted. If You institute patent litigation against any entity (including a
|
||||
cross-claim or counterclaim in a lawsuit) alleging that the Work or a
|
||||
Contribution incorporated within the Work constitutes direct or contributory
|
||||
patent infringement, then any patent licenses granted to You under this License
|
||||
for that Work shall terminate as of the date such litigation is filed.
|
||||
|
||||
4. Redistribution.
|
||||
|
||||
You may reproduce and distribute copies of the Work or Derivative Works thereof
|
||||
in any medium, with or without modifications, and in Source or Object form,
|
||||
provided that You meet the following conditions:
|
||||
|
||||
You must give any other recipients of the Work or Derivative Works a copy of
|
||||
this License; and
|
||||
You must cause any modified files to carry prominent notices stating that You
|
||||
changed the files; and
|
||||
You must retain, in the Source form of any Derivative Works that You distribute,
|
||||
all copyright, patent, trademark, and attribution notices from the Source form
|
||||
of the Work, excluding those notices that do not pertain to any part of the
|
||||
Derivative Works; and
|
||||
If the Work includes a "NOTICE" text file as part of its distribution, then any
|
||||
Derivative Works that You distribute must include a readable copy of the
|
||||
attribution notices contained within such NOTICE file, excluding those notices
|
||||
that do not pertain to any part of the Derivative Works, in at least one of the
|
||||
following places: within a NOTICE text file distributed as part of the
|
||||
Derivative Works; within the Source form or documentation, if provided along
|
||||
with the Derivative Works; or, within a display generated by the Derivative
|
||||
Works, if and wherever such third-party notices normally appear. The contents of
|
||||
the NOTICE file are for informational purposes only and do not modify the
|
||||
License. You may add Your own attribution notices within Derivative Works that
|
||||
You distribute, alongside or as an addendum to the NOTICE text from the Work,
|
||||
provided that such additional attribution notices cannot be construed as
|
||||
modifying the License.
|
||||
You may add Your own copyright statement to Your modifications and may provide
|
||||
additional or different license terms and conditions for use, reproduction, or
|
||||
distribution of Your modifications, or for any such Derivative Works as a whole,
|
||||
provided Your use, reproduction, and distribution of the Work otherwise complies
|
||||
with the conditions stated in this License.
|
||||
|
||||
5. Submission of Contributions.
|
||||
|
||||
Unless You explicitly state otherwise, any Contribution intentionally submitted
|
||||
for inclusion in the Work by You to the Licensor shall be under the terms and
|
||||
conditions of this License, without any additional terms or conditions.
|
||||
Notwithstanding the above, nothing herein shall supersede or modify the terms of
|
||||
any separate license agreement you may have executed with Licensor regarding
|
||||
such Contributions.
|
||||
|
||||
6. Trademarks.
|
||||
|
||||
This License does not grant permission to use the trade names, trademarks,
|
||||
service marks, or product names of the Licensor, except as required for
|
||||
reasonable and customary use in describing the origin of the Work and
|
||||
reproducing the content of the NOTICE file.
|
||||
|
||||
7. Disclaimer of Warranty.
|
||||
|
||||
Unless required by applicable law or agreed to in writing, Licensor provides the
|
||||
Work (and each Contributor provides its Contributions) on an "AS IS" BASIS,
|
||||
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied,
|
||||
including, without limitation, any warranties or conditions of TITLE,
|
||||
NON-INFRINGEMENT, MERCHANTABILITY, or FITNESS FOR A PARTICULAR PURPOSE. You are
|
||||
solely responsible for determining the appropriateness of using or
|
||||
redistributing the Work and assume any risks associated with Your exercise of
|
||||
permissions under this License.
|
||||
|
||||
8. Limitation of Liability.
|
||||
|
||||
In no event and under no legal theory, whether in tort (including negligence),
|
||||
contract, or otherwise, unless required by applicable law (such as deliberate
|
||||
and grossly negligent acts) or agreed to in writing, shall any Contributor be
|
||||
liable to You for damages, including any direct, indirect, special, incidental,
|
||||
or consequential damages of any character arising as a result of this License or
|
||||
out of the use or inability to use the Work (including but not limited to
|
||||
damages for loss of goodwill, work stoppage, computer failure or malfunction, or
|
||||
any and all other commercial damages or losses), even if such Contributor has
|
||||
been advised of the possibility of such damages.
|
||||
|
||||
9. Accepting Warranty or Additional Liability.
|
||||
|
||||
While redistributing the Work or Derivative Works thereof, You may choose to
|
||||
offer, and charge a fee for, acceptance of support, warranty, indemnity, or
|
||||
other liability obligations and/or rights consistent with this License. However,
|
||||
in accepting such obligations, You may act only on Your own behalf and on Your
|
||||
sole responsibility, not on behalf of any other Contributor, and only if You
|
||||
agree to indemnify, defend, and hold each Contributor harmless for any liability
|
||||
incurred by, or claims asserted against, such Contributor by reason of your
|
||||
accepting any such warranty or additional liability.
|
||||
|
||||
END OF TERMS AND CONDITIONS
|
||||
|
||||
APPENDIX: How to apply the Apache License to your work
|
||||
|
||||
To apply the Apache License to your work, attach the following boilerplate
|
||||
notice, with the fields enclosed by brackets "{}" replaced with your own
|
||||
identifying information. (Don't include the brackets!) The text should be
|
||||
enclosed in the appropriate comment syntax for the file format. We also
|
||||
recommend that a file or class name and description of purpose be included on
|
||||
the same "printed page" as the copyright notice for easier identification within
|
||||
third-party archives.
|
||||
BIN
packages/NPOI.2.6.2/NPOI.2.6.2.nupkg
vendored
Normal file
BIN
packages/NPOI.2.6.2/NPOI.2.6.2.nupkg
vendored
Normal file
Binary file not shown.
137
packages/NPOI.2.6.2/Read Me.txt
vendored
Normal file
137
packages/NPOI.2.6.2/Read Me.txt
vendored
Normal file
@@ -0,0 +1,137 @@
|
||||
================
|
||||
* Introduction *
|
||||
================
|
||||
This project is the .NET port of POI project. With NPOI, you can read/write Excel and Word files easily. It has a wide application.
|
||||
For example, you can use it a to generate a Excel report without Microsoft Office suite installed on your
|
||||
server and more efficient than call Microsoft Excel ActiveX at background; you can also use it to extract
|
||||
text from Office documents to help you implement full-text indexing feature (most of time this feature is
|
||||
used to create search engines).
|
||||
|
||||
=========================
|
||||
* Nissl Introduction *
|
||||
=========================
|
||||
NPOI was used to be maintained by Neuzilla ( Tony's first startup company). After Neuzilla is closed in 2018, Nissl Lab maintains NPOI.
|
||||
Nissl Lab is a NGO org created by Nissl LLC. The trademake NPOI is hold by Nissl in order to avoid abuse.
|
||||
|
||||
==================
|
||||
* NPOI Source Code *
|
||||
==================
|
||||
https://github.com/nissl-lab/npoi/
|
||||
|
||||
|
||||
==================
|
||||
* LICENSE COMPLIANCE *
|
||||
==================
|
||||
You are NOT allowed to remove NPOI logo or Nissl/Neuzilla brand (even text). This is a must of Apache license. This shows basic respects to the previous contributors of NPOI.
|
||||
You must state that you are using NPOI no matter you are creating a commercial product or an open source project.
|
||||
|
||||
======================
|
||||
* System Requirement *
|
||||
======================
|
||||
VS2015 and above
|
||||
medium trust environment in ASP.NET
|
||||
|
||||
=================
|
||||
* Nissl in social network *
|
||||
=================
|
||||
Linkedin: https://www.linkedin.com/company/nissl
|
||||
Github: https://github.com/nissl-lab
|
||||
|
||||
================
|
||||
* Team Members *
|
||||
================
|
||||
Tony Qu - coodinator, developer
|
||||
-------------------------------
|
||||
From: Shanghai, China
|
||||
Participated since Sep, 2008
|
||||
Time Zone: GMT+8
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
NPOI 1.2.1
|
||||
--------------------------------------------------------------------------------
|
||||
Huseyin Turfekcilerli - developer
|
||||
--------------------
|
||||
From: Istanbul, Turkey
|
||||
Participated since Nov, 2008
|
||||
Time Zone: GMT+2
|
||||
Main Contribution: POIFS Browser 1.0
|
||||
|
||||
aTao Xiang - Technical writer
|
||||
-----------
|
||||
From: China
|
||||
Participated since Aug, 2009
|
||||
Time Zone: GMT+8
|
||||
Main Contribution: NPOI 1.2 Chinese Tutorial
|
||||
|
||||
--------------------------------------------------------------------------------
|
||||
NPOI 1.2.3 - NPOI 1.2.5
|
||||
--------------------------------------------------------------------------------
|
||||
Antony - developer
|
||||
------------------------------
|
||||
From: Guangzhou, China
|
||||
Time Zone: GMT+8
|
||||
Main Contribution: main code,bug fixing ,Excel2Html, Word2Html
|
||||
|
||||
Christian Leutloff - developer
|
||||
------------------------------
|
||||
From: Germany
|
||||
Time Zone: GMT+1
|
||||
Main Contribution: fix FXCop warnings, OOXML
|
||||
|
||||
Jeff Stedfast - developer
|
||||
------------------------------
|
||||
From: Cambridge, MA, USA
|
||||
Time Zone: GMT
|
||||
Main contribution: Mono version of NPOI, naming conversion
|
||||
|
||||
Leon Wang - developer
|
||||
-----------------------------
|
||||
From: Xi'an, China
|
||||
Time Zone: GMT+8
|
||||
Main contribution: NPOIFS/POIFS
|
||||
|
||||
NPOI 2.0
|
||||
--------------------------------------------------------------------------------
|
||||
Tony Qu - chief developer
|
||||
-------------------------------
|
||||
From: Shanghai, China
|
||||
Time Zone: GMT+8
|
||||
Main Contribution: OpenXml4Net, OpenXmlFormats, NPOI.XSSF, NPOI.XWPF implementation
|
||||
|
||||
Antony - developer
|
||||
------------------------------
|
||||
From: Guangzhou, China
|
||||
Time Zone: GMT+8
|
||||
Main Contribution: XWPF implementation, OpenXmlFormats
|
||||
|
||||
Christian Leutloff - developer
|
||||
------------------------------
|
||||
From: Germany
|
||||
Time Zone: GMT+1
|
||||
Main Contribution: OpenXmlFormats, Excel 2007 comment read
|
||||
|
||||
Jeff Stedfast - developer
|
||||
------------------------------
|
||||
From: Cambridge, MA, USA
|
||||
Time Zone: GMT
|
||||
Main contribution: Mono version of NPOI, enumeration changes and compilation optimization
|
||||
|
||||
Paul Kratt - developer
|
||||
------------------------------
|
||||
From: Greater Milwaukee Area, Wisconsin, USA
|
||||
Time Zone: GMT
|
||||
Main contribution: CopyTo, CopySheet functions in HSSFSheet
|
||||
|
||||
NPOI 2.1
|
||||
--------------------------------------------------------------------------------
|
||||
Tony Qu - main contributor
|
||||
Antony - fix some poi bugs
|
||||
|
||||
Phil Rykoff - developer
|
||||
------------------------------
|
||||
Main contribution: XSSF bug fixing and feature implement
|
||||
|
||||
NPOI 2.2 ~ 2.5.2
|
||||
--------------------------------------------------------------------------------
|
||||
Antony
|
||||
Tony Qu
|
||||
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.Core.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.Core.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.Core.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.Core.pdb
vendored
Normal file
Binary file not shown.
46706
packages/NPOI.2.6.2/lib/net472/NPOI.Core.xml
vendored
Normal file
46706
packages/NPOI.2.6.2/lib/net472/NPOI.Core.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OOXML.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OOXML.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OOXML.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OOXML.pdb
vendored
Normal file
Binary file not shown.
12623
packages/NPOI.2.6.2/lib/net472/NPOI.OOXML.xml
vendored
Normal file
12623
packages/NPOI.2.6.2/lib/net472/NPOI.OOXML.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXml4Net.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXml4Net.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXml4Net.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXml4Net.pdb
vendored
Normal file
Binary file not shown.
3221
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXml4Net.xml
vendored
Normal file
3221
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXml4Net.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXmlFormats.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXmlFormats.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXmlFormats.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXmlFormats.pdb
vendored
Normal file
Binary file not shown.
4966
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXmlFormats.xml
vendored
Normal file
4966
packages/NPOI.2.6.2/lib/net472/NPOI.OpenXmlFormats.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.Core.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.Core.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.Core.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.Core.pdb
vendored
Normal file
Binary file not shown.
46733
packages/NPOI.2.6.2/lib/net6.0/NPOI.Core.xml
vendored
Normal file
46733
packages/NPOI.2.6.2/lib/net6.0/NPOI.Core.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OOXML.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OOXML.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OOXML.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OOXML.pdb
vendored
Normal file
Binary file not shown.
12623
packages/NPOI.2.6.2/lib/net6.0/NPOI.OOXML.xml
vendored
Normal file
12623
packages/NPOI.2.6.2/lib/net6.0/NPOI.OOXML.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXml4Net.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXml4Net.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXml4Net.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXml4Net.pdb
vendored
Normal file
Binary file not shown.
3221
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXml4Net.xml
vendored
Normal file
3221
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXml4Net.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXmlFormats.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXmlFormats.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXmlFormats.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXmlFormats.pdb
vendored
Normal file
Binary file not shown.
4966
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXmlFormats.xml
vendored
Normal file
4966
packages/NPOI.2.6.2/lib/net6.0/NPOI.OpenXmlFormats.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.Core.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.Core.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.Core.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.Core.pdb
vendored
Normal file
Binary file not shown.
46706
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.Core.xml
vendored
Normal file
46706
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.Core.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OOXML.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OOXML.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OOXML.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OOXML.pdb
vendored
Normal file
Binary file not shown.
12623
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OOXML.xml
vendored
Normal file
12623
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OOXML.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXml4Net.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXml4Net.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXml4Net.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXml4Net.pdb
vendored
Normal file
Binary file not shown.
3221
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXml4Net.xml
vendored
Normal file
3221
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXml4Net.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXmlFormats.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXmlFormats.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXmlFormats.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXmlFormats.pdb
vendored
Normal file
Binary file not shown.
4966
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXmlFormats.xml
vendored
Normal file
4966
packages/NPOI.2.6.2/lib/netstandard2.0/NPOI.OpenXmlFormats.xml
vendored
Normal file
File diff suppressed because it is too large
Load Diff
BIN
packages/NPOI.2.6.2/lib/netstandard2.1/NPOI.Core.dll
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.1/NPOI.Core.dll
vendored
Normal file
Binary file not shown.
BIN
packages/NPOI.2.6.2/lib/netstandard2.1/NPOI.Core.pdb
vendored
Normal file
BIN
packages/NPOI.2.6.2/lib/netstandard2.1/NPOI.Core.pdb
vendored
Normal file
Binary file not shown.
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user